The reality for engineering teams
Production infrastructure becomes a liability before anyone notices
Engineering teams in regulated industries don't set out to own a platform. But as the product grows, the AWS stack someone built in the early days starts requiring full-time attention, with compliance and security overhead compounding on top of it. These are the failure modes we see most often.
One engineer becomes the accidental platform owner
The AWS stack was never supposed to be a full-time job. But every compliance question, infrastructure incident, and security review flows through whoever built it. The rest of the team can't ship without them, and that person is stuck on call for infrastructure decisions instead of product work.
Compliance prep costs unplanned engineering sprints
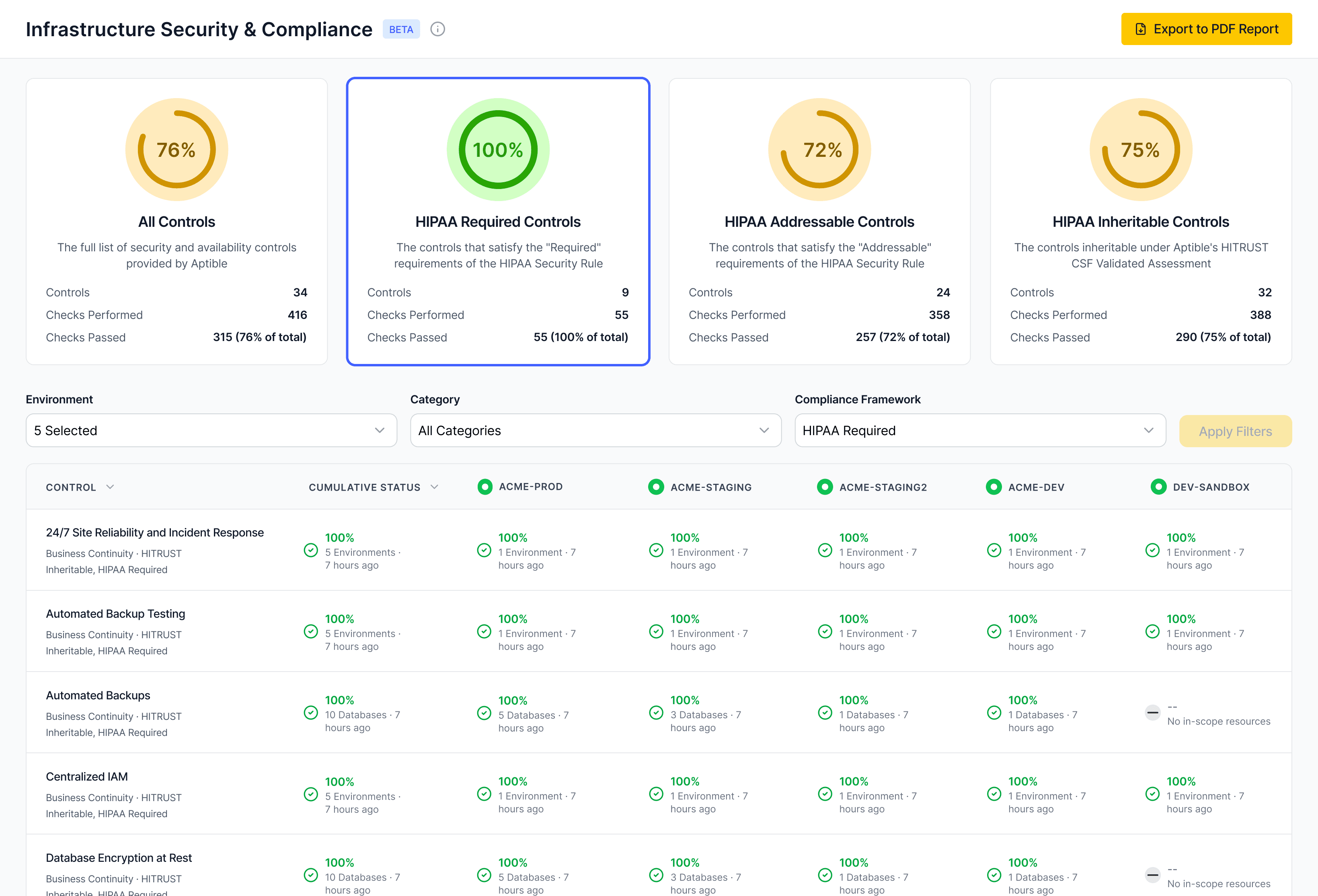
SOC 2, HIPAA audits, and enterprise security reviews arrive on short notice and land on engineering. Pulling logs, verifying access controls, documenting what the stack actually does... it takes weeks and none of it was in the roadmap. The process repeats every time a new review arrives.
Controls drift as the system grows
The original setup was careful. But as new services, environments, and engineers are added, IAM policies widen, logging coverage becomes inconsistent, and isolation assumptions break down. The drift is invisible until an auditor or enterprise customer asks a question the team can't answer cleanly.
New services inherit no defaults
Adding a new application, worker, or database means reconfiguring network boundaries, access controls, and logging from scratch. There's no template that carries the security model forward: just another set of decisions to get right under time pressure.
Enterprise deals stall on infrastructure questions
A sale is about to close. Then the security questionnaire arrives and it goes to engineering. Who has production access? How long are logs retained? How is PHI isolated? When did the last configuration change happen? Finding complete, attributable answers takes longer than anyone expected, and deals wait.
Scale the product without scaling the platform team
Add applications, services, and databases as the product grows without adding infrastructure headcount or inheriting new operational debt.
Pass security reviews without a sprint of prep
Answer diligence questions about access history, PHI isolation, encryption, and log retention directly from the platform, without reconstructing evidence after the fact.
Add services safely without redefining the security model
Introduce new components to the stack without reconfiguring network boundaries, rebuilding access controls, or starting logging from scratch.
Keep controls consistent as the team and system change
Enforce least-privilege access and auditability as engineers join, leave, and change roles. Controls hold without requiring manual review cycles to catch what drifted.