What goes wrong in digital health
The moment PHI enters your system, you’re operating under HIPAA
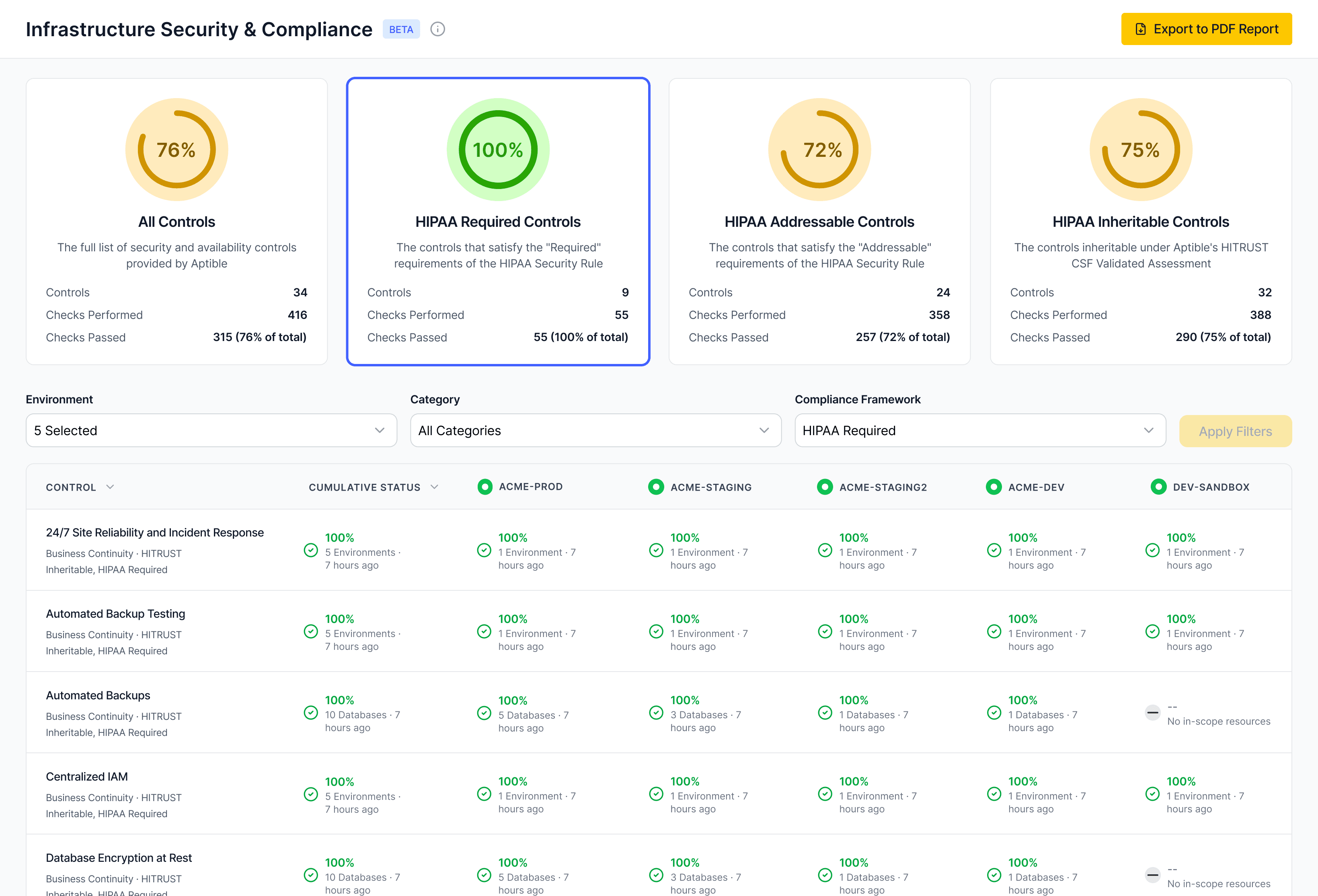
Early infrastructure decisions become compliance liabilities, causing teams to spend months on rework. These are the five failure modes we see most frequently.
Non-prod becomes in-scope
Staging turns into production. A support escalation needs “a real example,” so someone copies a production row into staging. A demo environment quietly keeps real patient data because “we’ll delete it later.” It rarely gets deleted.
Access expands and never retracts
“Temporary admin” becomes permanent. A contractor gets broad access for a migration. A break-glass key gets shared in Slack during an incident. A CI token that can read everything stays alive long after the fire is out.
Documentation drifts from reality
Docs say one thing, infra does another. The security policy says “least privilege,” but IAM roles are wide because tightening them breaks deploys. The runbook says “logs retained,” but retention depends on a tool nobody owns.
Customer security reviews force archaeology
You’re asked to prove, not promise. Buyers ask: “Show me who accessed production,” “How long are logs retained,” “What changed last week,” “Where does PHI go,” “What’s your incident process.” Deals stall or fail because teams can’t produce complete, attributable evidence on demand.
Deploy PHI workloads
Run apps, databases, and AI with encryption, isolation, access logging, and least-privilege IAM enforced by default.
Add services safely
Introduce new apps, workers, databases, or AI endpoints without redefining network boundaries, rewriting IAM, or rebuilding your logging model.
Produce audit artifacts
Export access history, change events, backup posture, and retention settings directly from the platform.
Pass security reviews
Answer diligence questions about PHI flow, isolation, access, and incident response without re-architecting your stack.