Documentation Index
Fetch the complete documentation index at: https://www.aptible.com/docs/llms.txt
Use this file to discover all available pages before exploring further.
aptible endpoints:tls:create command.
Traffic
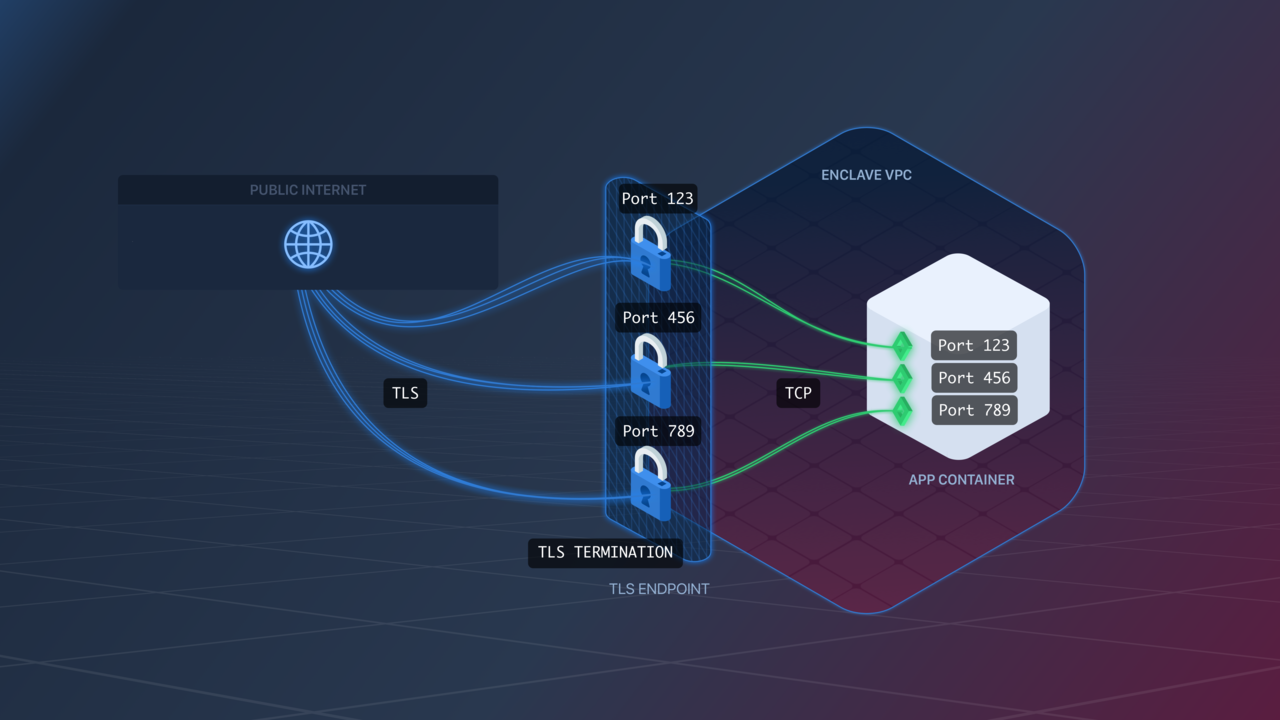
TLS Endpoints terminate TLS traffic and transfer it as plain TCP to your app.Container Ports
TLS Endpoints are configured similarly to TCP Endpoints. The Endpoint will listen for TLS traffic on exposed ports and transfer it as TCP traffic to your app over the same port. For example, if your Image exposes port123, the Endpoint will listen for TLS traffic on port 123, and forward it as TCP traffic to your app Containers on port 123.
Idle Timeout
TLS Endpoints enforce an idle timeout on connections. By default, the inactivity timeout is 60 seconds. You can configure a different timeout per endpoint:idle_timeout on the aptible_endpoint resource (see Endpoint Settings).
SSL / TLS Settings
Aptible offers a few ways to configure the protocols used by TLS endpoints for TLS termination.SSL Protocols Override
The SSL Protocols Override setting lets you customize the SSL/TLS protocols allowed on your Endpoint.- For TLS Endpoints: you can choose from these combinations:
TLSv1 TLSv1.1 TLSv1.2(default)TLSv1.1 TLSv1.2TLSv1.2TLSv1.3
SSL Ciphers Override
This setting lets you customize the SSL ciphers used by your Endpoint. The format is a string accepted by Nginx for its ssl_ciphers directive. Pay very close attention to the required format, as a bad value will prevent the proxies from starting.Disable Weak Cipher Suites
Enabling this setting causes your Endpoint to stop accepting traffic over theSSLv3 protocol or using the RC4 cipher.
We strongly recommend enabling this on all TLS Endpoints.
Examples
Set Idle Timeout
Set SSL Protocols Override
Disable Weak Cipher Suites
ssl_protocols_override, ssl_ciphers_override, and disable_weak_cipher_suites on the aptible_endpoint resource (see Endpoint Settings).

